About
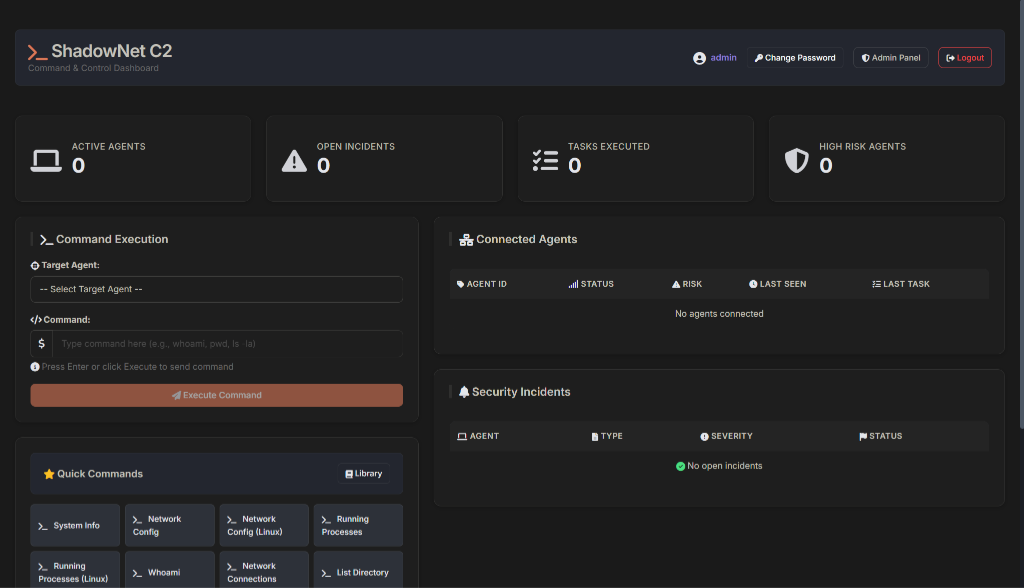
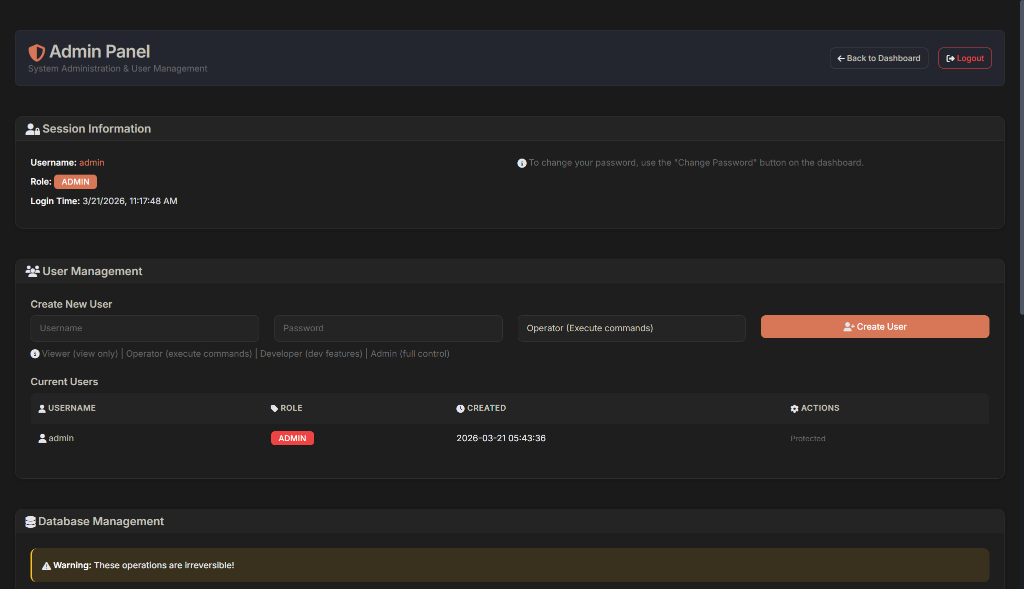
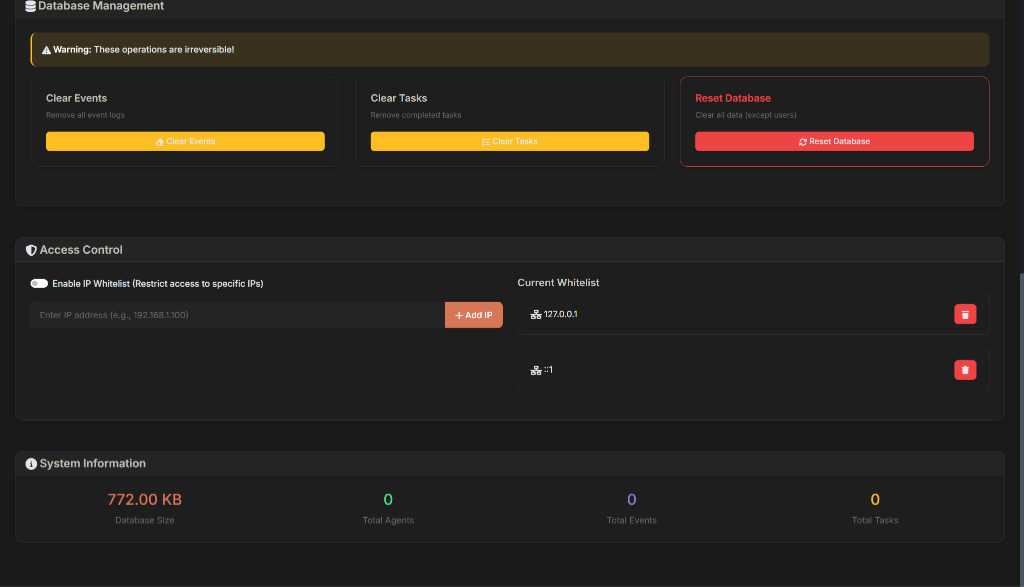
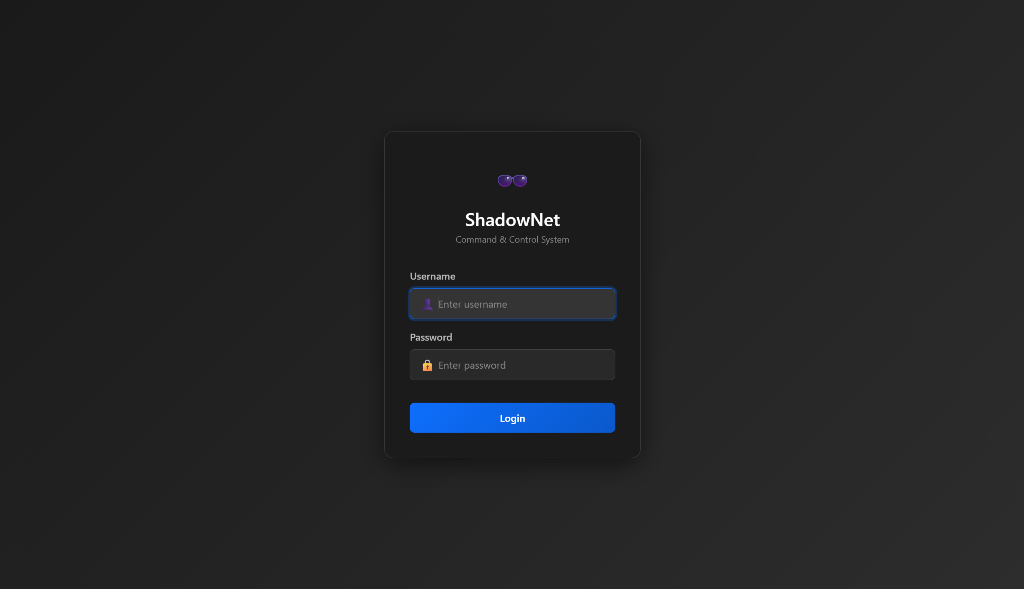
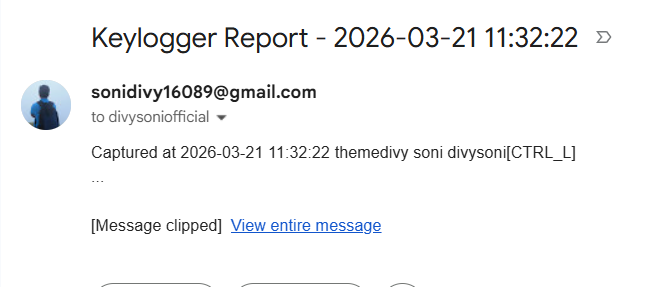
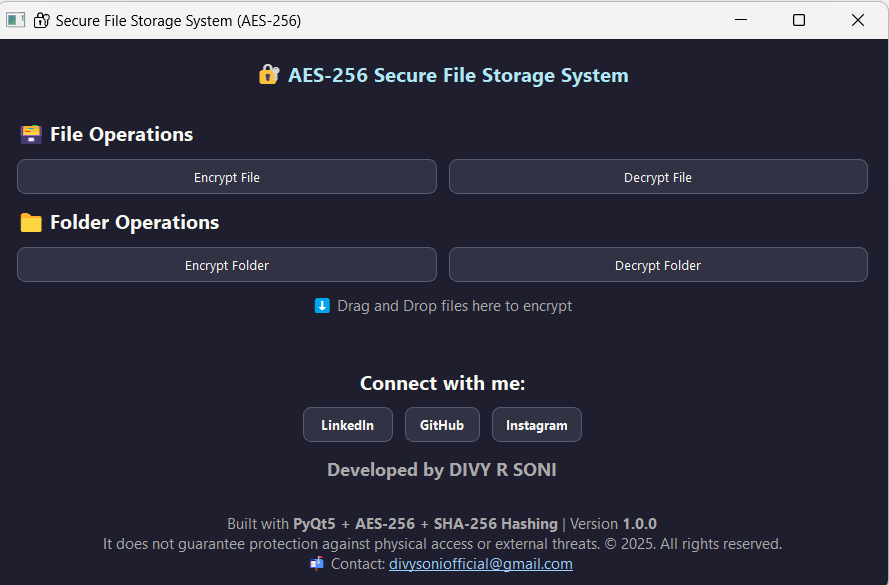
Cybersecurity specialist with a focus on offensive security, cryptography, and secure system architecture. Experienced in developing advanced Command & Control frameworks (like ShadowNet C2), encrypted keyloggers, and decentralized file storage solutions. I bridge the gap between software engineering and red teaming to discover critical vulnerabilities and build robust tools.✔ Analyzing Penetration Testing metrics...✔ Auditing Cryptography & Secure Architecture...✔ Checking Command & Control Frameworks...Check out my latest work
I've worked on a variety of projects, from simple websites to complex web applications. Here are a few of my favorites.
Continuous Learning
I am dedicated to continuous education and skill improvement. I have completed 4+ specialized courses and certifications to stay at the cutting edge of the industry.
Certified Flicker Security Associate (CFSA)
Flicker Security
Certificate ID: FTC25CFSAXXX1. Validated knowledge of Network Security and Cybersecurity Fundamentals. Gained hands-on skills in: Pentesting fundamentals, Threat landscape analysis, SOC workflows, Log analysis and monitoring, and Defensive cybersecurity strategies.

SOC Level 1
TryHackMe
Comprehensive pathway focusing on Security Operations Center (SOC) workflows, working with SIEMs, Digital Forensics, Incident Response, and Threat Intelligence.

Jr Penetration Tester
TryHackMe
Comprehensive learning path covering Pentesting methodology, Exploitation, and Industry tools (Nmap, Burp Suite).

Web Fundamentals
TryHackMe
Learning path focusing on Web security basics, OWASP, Input validation, and Hands-on labs.
Skills & Tech Stack
Get in Touch
Want to chat? Just shoot me an email with a direct question and I'll respond whenever I can. I will ignore all soliciting.